Since we started, iSupportU has evolved from providing basic computer repair services to individuals, to delivering full IT support and services to people and companies. Our approach has always been to focus on de-mystifying the information technology issues people face and operate in an environmentally aware and sustainable way. But, deep down, we knew there was even more that our business could do. And there was.
 iSupportU is proud to have become a Certified B Corporation, or B Corp. We are committed to being a for-profit business that is dedicated to social and environmental issues. Sure, the words “social” and “environmental” are how you may have heard many companies describe themselves. For us, it was critical that these words not only express who we already are, but we also wanted to invest and commit to making these traits formal aspects of our organization.
iSupportU is proud to have become a Certified B Corporation, or B Corp. We are committed to being a for-profit business that is dedicated to social and environmental issues. Sure, the words “social” and “environmental” are how you may have heard many companies describe themselves. For us, it was critical that these words not only express who we already are, but we also wanted to invest and commit to making these traits formal aspects of our organization.
B Corp certification is granted by B Lab, a U.S.-based nonprofit that serves a global movement working to transition companies from being the best in the world to being the best for the world. The vision is grand, but the belief is practical.
By encouraging organizations voluntarily to examine their role in a larger community, businesses have the opportunity to ensure their operations align with their beliefs. iSupportU started with this premise from its inception, so we were delighted to discover that there was a certifiable process that both acknowledges our approach and gives us a way to integrate this officially into our organization.
The process of B Corp certification was rigorous and took many months to achieve. iSupportU was evaluated on a range of operational aspects from energy efficiency to environmental performance to social and legal accountability. Following a phone interview with company leadership, we submitted documentation supporting our efforts and policies. We took the opportunity also to reevaluate and adjust our operating principles to ensure our commitment was evident.
The areas we have been evaluated on, and the commitment our organization has shown, are important to our company. To be certified that we meet the highest standards demonstrates to our many partners that they can rely on the best quality service delivered with the maximum commitment to positive social and environmental impact.

What does B Corp certification mean for our customers, employees, vendors, and stakeholders? We believe it means a lot. Not unlike companies that receive a USDA Organization certification for milk or buildings that achieve a U.S. Green Building Council LEED certification, certified B Corp companies show commitment and provide assurance to everyone that works with us that we are committed to something above and beyond profits. We are proud to be part of about 1,600 companies from 42 countries around the world that make up the growing B Corp certification network.
But it’s not over. Because the process for certification is strenuous and must be regularly certified (B Lab doesn’t expect any organization ever to achieve the highest score), we are continually striving to look for ways and areas in which to improve. We seek opportunities to raise our social and environmental performance as well as increase our transparency and accountability. When it comes to reaching a high level of standard of practice, there’s always more to do, and we embrace this.
From the outset, we were committed to providing exceptional IT service and support, but we also knew we could offer more and be a better company. iSupportU sought to be an organization that could achieve continuous business, environmental, and social improvement. B Corp certification provides not an end to reaching this goal, but a roadmap to reach a destination. And that really matters.



 The first step in selecting any service provider for your business, whether it be an IT services company or any other provider, is to know what you’re looking for. Such criteria of course include verifiable competence, experience and track record, reliability and punctuality, and adherence to industry standard rates (i.e. won’t surprise you with outrageous invoices). You want a provider with talent, training, and experience to take care of your business needs, especially when it comes to IT!
The first step in selecting any service provider for your business, whether it be an IT services company or any other provider, is to know what you’re looking for. Such criteria of course include verifiable competence, experience and track record, reliability and punctuality, and adherence to industry standard rates (i.e. won’t surprise you with outrageous invoices). You want a provider with talent, training, and experience to take care of your business needs, especially when it comes to IT!
 Purchase a USB drive, or an external hard drive that’s easy to use. Simply plug the device into your PC or Mac; identify which files and folders to backup; and start the backup process. It’s important to note that not all USB drives are created equal, so be sure to do your research and find a quality option that features plenty of storage space. USB drives are one of your ‘local’ backup options that allow you to store your data, take it with you, or stow away for safekeeping.
Purchase a USB drive, or an external hard drive that’s easy to use. Simply plug the device into your PC or Mac; identify which files and folders to backup; and start the backup process. It’s important to note that not all USB drives are created equal, so be sure to do your research and find a quality option that features plenty of storage space. USB drives are one of your ‘local’ backup options that allow you to store your data, take it with you, or stow away for safekeeping. Create a cloud backup, which stores your files online and allows you to access them anytime, anywhere. Password creation is generally part of the process to keep your files secure. Cloud backup is celebrated as one of the most secure and easily accessible (accessible to you, that is) methods available, but it generally requires paying for a subscription. A subscription isn’t the worst thing when it comes to data backup, however. According to
Create a cloud backup, which stores your files online and allows you to access them anytime, anywhere. Password creation is generally part of the process to keep your files secure. Cloud backup is celebrated as one of the most secure and easily accessible (accessible to you, that is) methods available, but it generally requires paying for a subscription. A subscription isn’t the worst thing when it comes to data backup, however. According to Remember, whatever backup means you select, it’s important to stay organized. If you consistently keep your files and data well ordered, you’ll know exactly what requires recovery and can easily put items back where they belong.
Remember, whatever backup means you select, it’s important to stay organized. If you consistently keep your files and data well ordered, you’ll know exactly what requires recovery and can easily put items back where they belong.
 The obvious benefits of a wireless network is the lack of physical wires! We all know that familiar feeling of waging war with a tangled mess of wires. A wireless network is easy to use and accommodates changes in a network without cords and cables. Adding new desks and employees? A wireless network is the easiest logistical choice.
The obvious benefits of a wireless network is the lack of physical wires! We all know that familiar feeling of waging war with a tangled mess of wires. A wireless network is easy to use and accommodates changes in a network without cords and cables. Adding new desks and employees? A wireless network is the easiest logistical choice.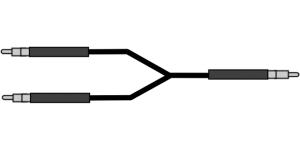 A wired network obviously incorporates physical network into the data connection. The wires enable increased security, control, reliability, and speed. Using physical connections might not seem as advances as the wireless alternative, but it is the superior choice when your data is precious and confidential. If your business values security over hip trends in tech, a wireless network is the obvious choice.
A wired network obviously incorporates physical network into the data connection. The wires enable increased security, control, reliability, and speed. Using physical connections might not seem as advances as the wireless alternative, but it is the superior choice when your data is precious and confidential. If your business values security over hip trends in tech, a wireless network is the obvious choice.